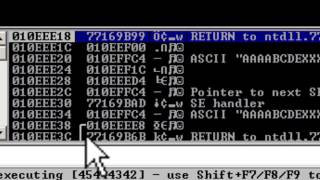
Media Summary: Buffer-Overflow Attack demonstrated by SRIVATSAN V A college lecture at City College San Francisco. Based on "The Shellcoder's Handbook: Discovering and Exploiting Security ... So yeah so that is a pretty simplified example of
Server 2008 Buffer Overflow Attack Ethical Hacking Part 15 - Detailed Analysis & Overview
Buffer-Overflow Attack demonstrated by SRIVATSAN V A college lecture at City College San Francisco. Based on "The Shellcoder's Handbook: Discovering and Exploiting Security ... So yeah so that is a pretty simplified example of Ethical Hacking Beginners Tutorial 43 Hack a System PC using Buffer Overflow Attack 720p 30fps H THE OFFICIAL VIDEO COMPANION GUIDE TO 'BECOME AN Buffer Overflow Attack, DNS Poisoning Attack
This is the recording of our previously conducted webinar on How This Video only for education purpose. 1. We updated this video for accuracy and improved graphics. Please view the new version here: Hacking Demo - Buffer Overflow, Shellcode, Webshell (edit with subtitles)