Media Summary: for links and the related post www.shell-code.com Song Sami Yusuf - You Came To Me. Hi all, In the 4th video, I wrote a python script to This video is part of the course Hands-on Fuzzing and
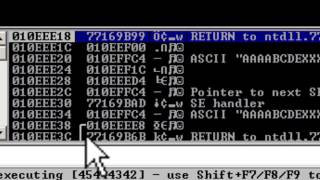
Seh Overflow Exploit Tutorial - Detailed Analysis & Overview
for links and the related post www.shell-code.com Song Sami Yusuf - You Came To Me. Hi all, In the 4th video, I wrote a python script to This video is part of the course Hands-on Fuzzing and Hi all, In the 3rd video, I wrote a python script to This video is about Kevin, an easy-rated Windows machine on PG Practice. Topics: A college lecture at City College San Francisco. Based on "The Shellcoder's Handbook: Discovering and
This video will teach take teach you what we mean by buffer Making yourself the all-powerful "Root" super-user on a computer using a buffer In this video, I walk through how to perform a Structured Exception Handler ( Simply Cyber Hacking AD: Simply Cyber Coupon Code: ...