Media Summary: Ready to become a certified Professional Architect? Register now and use code IBMTechYT20 for 20% off of your exam ... Ready to become a certified SOC Analyst - QRadar SIEM V7.5 Plus CompTIA Cybersecurity Analyst? Register now and use code ... ... compliance many data scientists and teams are required to explain their
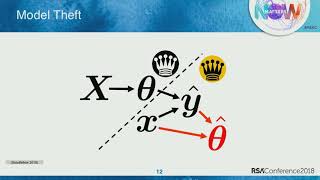
Securing Machine Learning Models - Detailed Analysis & Overview
Ready to become a certified Professional Architect? Register now and use code IBMTechYT20 for 20% off of your exam ... Ready to become a certified SOC Analyst - QRadar SIEM V7.5 Plus CompTIA Cybersecurity Analyst? Register now and use code ... ... compliance many data scientists and teams are required to explain their Ready to become a certified Guardium Data Protection v12.x Administrator - Professional? Register now and use code ... Data poisoning, invisible adversarial attacks, and massive privacy leaks are the biggest threats facing modern AI. Your sensitive ... There's been a lot of buzz going on in the
In this webinar, Professor Dan Boneh discusses recent work at the intersection of cybersecurity and Welcome to the ultimate guide on Centrify API Ready to become a certified watsonx Generative AI Engineer? Register now and use code IBMTechYT20 for 20% off of your exam ... Ian Goodfellow, Staff Research Scientist, Google Brain Combatting output integrity attack is one of the major miltstones to be achieved in an attempt to build a