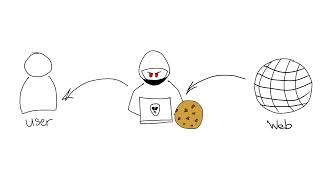
Media Summary: Discover how modern Man-in-the-Middle (MitM) and Adversary-in-the-Middle ( In this eye-opening video, we delve into the dark world of cybersecurity as we demonstrate how Want to uncover the latest insights on ransomware, dark web threats, and AI risks? Read the 2024 Threat Intelligence Index ...
S1e5 How Hackers Bypass Mfa Aitm Attacks Explained 1080p Caption - Detailed Analysis & Overview
Discover how modern Man-in-the-Middle (MitM) and Adversary-in-the-Middle ( In this eye-opening video, we delve into the dark world of cybersecurity as we demonstrate how Want to uncover the latest insights on ransomware, dark web threats, and AI risks? Read the 2024 Threat Intelligence Index ... Resources: Enroll in my Courses (search for Tyler Ramsbey) Support me on Ko-Fi ... Evilginx lets attackers steal logins and session cookies to In this video, I demonstrate how attackers can
In this video, we delve into the tactics employed by W3LL was a $500 phishing-as-a-service platform that fundamentally changed how attackers In this cybersecurity awareness demonstration, I show how attackers can Are you relying solely on two-factor authentication (2FA) to keep your online accounts safe? Think again! In this eye-opening ... Learn how to use Prompt Injection to Jailbreak and hack AI through a series of gamified practical labs. Material Security: ...