Media Summary: Please Subscribe Thank you Linkedin THM-Attacker Tryhackme! Task 5 run ... In this video walkthrough, we covered the concept of Don't miss out! Join us at our next Flagship Conference: KubeCon + CloudNativeCon North America in Salt Lake City from ...
Runtime Detection Evasion - Detailed Analysis & Overview
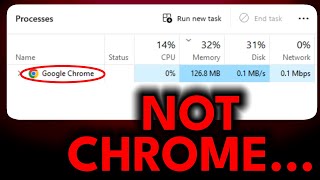
Please Subscribe Thank you Linkedin THM-Attacker Tryhackme! Task 5 run ... In this video walkthrough, we covered the concept of Don't miss out! Join us at our next Flagship Conference: KubeCon + CloudNativeCon North America in Salt Lake City from ... EDUCATIONAL PURPOSES ONLY Task manager is no bueno for telling you information about programs, this video goes over 3 ... Oh okay thank you Thank you Okay so before we start we need to understand how Ready to become a certified watsonx Generative AI Engineer - Associate? Register now and use code IBMTechYT20 for 20% off ...
The rapid expansion of the Internet of Things (IoT) has brought unprecedented convenience and integration to our homes, ... Welcome to the official showcase of FireflyProtector, a comprehensive security solution designed to safeguard software integrity ... In this video walk-through, we covered debugging as a method to uncover In the current digital security ecosystem, where threats evolve rapidly and with complexity, companies developing Endpoint ... Introduction to Shellcode Learn shellcode encoding, packing, binders, and crypters. Bypass Windows Defender 2023 Bypass Windows Defender