Media Summary: Not every login is the same, so why treat them that way? Every keystroke, click, and move shapes your digital identity—behavioural analytics powers ... friction with end-users and make it simple and quick for users to securely log in to services using
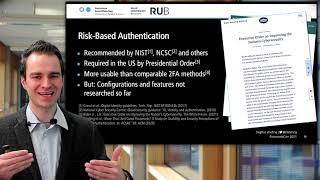
Risk Based Authentication In Real Time - Detailed Analysis & Overview
Not every login is the same, so why treat them that way? Every keystroke, click, and move shapes your digital identity—behavioural analytics powers ... friction with end-users and make it simple and quick for users to securely log in to services using CiscoDuo While you need to verify trust, you also need to evaluate and respond to ... Passwords aren't enough anymore, security needs to think smarter. Dive into how Forget the old firewall fortress, zero trust and
Looking to boost your MFA without annoying your users? OWASP Vancouver Presentations 2019-01-24 (Part 2) *** Your organization does not have to be breached for you to end up ... Most organizations still rely on static MFA and siloed systems, creating unnecessary friction for trusted users while leaving gaps ... Castle is helping businesses keep customers' online accounts safe from targeted account takeovers, automated credential stuffing ... USENIX Security '23 - A Study of Multi-Factor and