Media Summary: Digital Signal Analysis for Hardware Hackers training: ... In this video, I cover the most important basics of The government doesn't want you to know this but the
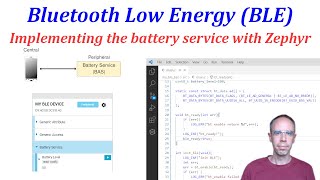
Reverse Engineering Bluetooth Low Energy Ble Devices - Detailed Analysis & Overview
Digital Signal Analysis for Hardware Hackers training: ... In this video, I cover the most important basics of The government doesn't want you to know this but the Quick preview of a fun hack I've been working on to This talk describes my process of going from knowing nothing about What is going on all right so I want to show you how we are using
... OS Fingerprinting, and Behavioral Profiling We This content is from a talk I gave at CornCon 8. It will be separated into 3 parts: Part 1: Intro to Join us for our monthly meetup and an evening exploring