Media Summary: Security+ Training Course Index: Professor Messer's Course Notes: ... Welcome to Shree Learning Academy! In this video, we explore the concept of Blockchain forks can create duplicate coins, but they also open the door to
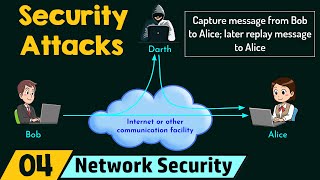
Replay Attacks Explained - Detailed Analysis & Overview
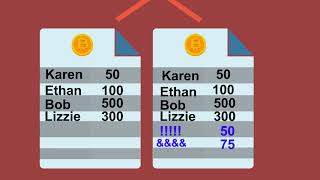
Security+ Training Course Index: Professor Messer's Course Notes: ... Welcome to Shree Learning Academy! In this video, we explore the concept of Blockchain forks can create duplicate coins, but they also open the door to Imagine a hacker taking your valid transaction and playing it again to steal funds. In this CodeAccessHub security deep dive, ... Welcome to our latest video, where we delve into the critical topic of Welcome to Shree Learning Academy! In this video, we will explore the concept of
Imagine your access card wasn't stolen — it was replayed. This explainer walks cybersecurity students through Wireless Please donate to 13VL192v5y8fWdMdRk7eGduBmcH7CQDWdM to support this video. When we reach 0.15 BTC we will produce ... Bitcoin's history is full of hardforks, I try to bring some of the most important ones in this video and show the issue with possible ... Simple test to open and close Hyundai Tucson's doors (my own car of course) using HackRF One tool that previously captured the ...