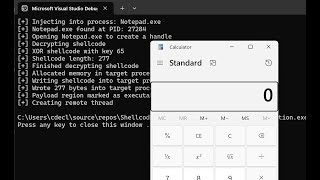
Media Summary: Hello everyone! Hope you all are doing well! Today I'll be teaching you Disclaimer: This video is only for educational purpose just to educate you and aware you about this type of attack. I hope you will ... Only legal, educational and legitimate uses of the code / principles shown in the video are condoned. I am not responsible for how ...
Remote Process Injection C Tutorial C Malware Development - Detailed Analysis & Overview
Hello everyone! Hope you all are doing well! Today I'll be teaching you Disclaimer: This video is only for educational purpose just to educate you and aware you about this type of attack. I hope you will ... Only legal, educational and legitimate uses of the code / principles shown in the video are condoned. I am not responsible for how ... In this installment of Reverse Reverse Engineering, I make some minor changes to the This is a continuation of the series where I will share the basics of Join this channel to get access to perks: