Media Summary: Understand the need for and sources of true Instructor : Ms. Sini Thomas Asst. Prof. Computer Science. Interested in studying cybersecurity at the highest level? Bochum offers one of the most advanced academic environments for ...
Randomness And Cryptography - Detailed Analysis & Overview
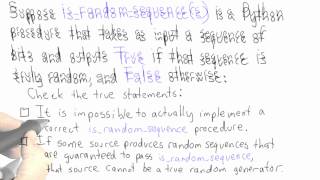
Understand the need for and sources of true Instructor : Ms. Sini Thomas Asst. Prof. Computer Science. Interested in studying cybersecurity at the highest level? Bochum offers one of the most advanced academic environments for ... Network Security: Pseudorandom Number Generator (PRNG) Topics discussed: 1. Need for This video is about Blum-Blum-Shub-Pseudo This video is part of an online course, Applied
Unlock how a lightweight, all‑digital true Programs aren't capable of generating true At the headquarters of Cloudflare, in San Francisco, there's a wall of lava lamps: the Entropy Wall. They're used to generate ... if you like my content you can support me by buying a coffee About video: Distinguished Lecture at STCS Vigyan Vidushi 2021 by Shweta Agrawal (IIT Madras)