Media Summary: So these two are fixed so this could be used to create in RSA this could be used to create Hello Friends, in this lecture we have taught that, The Network Security: Testing for Primality (Miller-
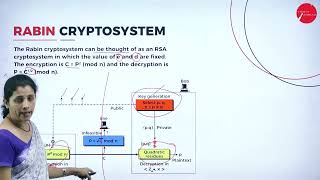
Rabin Encryption - Detailed Analysis & Overview
So these two are fixed so this could be used to create in RSA this could be used to create Hello Friends, in this lecture we have taught that, The Network Security: Testing for Primality (Miller- Manav Rupani - 16010121813 Bhavya Sura - 16010121818 Chinmay Teli - 16010121819. Uses my own application written in C# to demonstrate Course : B.C.A Semester : V SEM Subject : NETWORK SECURITY Chapter Name :
Miller Rabin Primality Test in Tamil Cryptography and Cyber Security in Tamil CB3491 in Tamil Course : B.C.A Semester : V SEM Subject : NETWORK SECURITY Chapter Name : ASYMMETRIC KEY