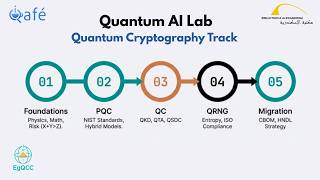
Media Summary: Okay so when it comes to Quantum as I said you have pqc which is post Try as we might, malicious actors can sometimes outsmart classical So there are several evidences or for reasons to support our proposal of basing a
Quantum Cryptography Session 2 - Detailed Analysis & Overview
Okay so when it comes to Quantum as I said you have pqc which is post Try as we might, malicious actors can sometimes outsmart classical So there are several evidences or for reasons to support our proposal of basing a Are our digital secrets truly safe in the age of Recorded 27 July 2022. Anne Broadbent of the University of Ottawa presents "Information-Theoretic Ready to become a certified watsonx AI Assistant Engineer? Register now and use code IBMTechYT20 for 20% off of your exam ...