Media Summary: In CyberVista's Questions That Need Answers ( Watch this Radware Minute episode with Radware's Eva Abergel to learn what is a TCP In this video we will learn about how to detect
Qtna 30 Syn Flood - Detailed Analysis & Overview
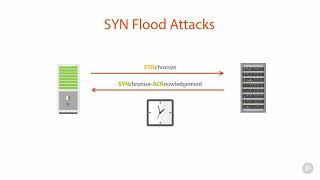
In CyberVista's Questions That Need Answers ( Watch this Radware Minute episode with Radware's Eva Abergel to learn what is a TCP In this video we will learn about how to detect This is something I did over a month ago for fun. I've always wondered how to perform a cyber attack and I guess this is the first ... Join us as we dissect this common yet potent cyber threat, understanding its mechanics, impact on systems, and crucial strategies ... 11.6.8 Analyze a SYN Flood Attack : TestOut
What is IP Spoofing - To the Point Explanation in URDU/HINDI NETWORK ... Command used: ° netstat -na grep tcp ° sudo sysctl -a grep syncookie ° sudo sysctl -w net.ipv4.tcp_syncookies=0 ° sudo netwox ... Start learning cybersecurity with CBT Nuggets. In this video, Keith Barker covers what TCP In this lecture we will be looking at 1. What is a DOS Attack 2. What is Ping Lab Scenario : DoS attacks are a kind security break that does not generally result in the theft of information. However, these ...