Media Summary: Link to the Box folder with the index to more Hello I'm Aniketwa and today we'll be discussing testing protocols using lock Hello everyone, thank you kindly for watching, hope you enjoyed! This course is a direct reupload from my original Udemy course, ...
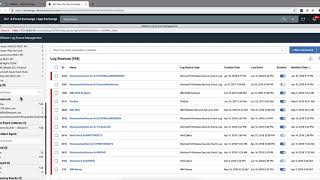
Qradar Log Source Management App V3 - Detailed Analysis & Overview
Link to the Box folder with the index to more Hello I'm Aniketwa and today we'll be discussing testing protocols using lock Hello everyone, thank you kindly for watching, hope you enjoyed! This course is a direct reupload from my original Udemy course, ... ... our to curator curator out to discover the Rules created by Security Analysts can sometimes be resource intensive and thus lead to performance degradation at CRE stage ... This video helps to configure Linux OS to send audit
When you enable Property Autodetection, new properties are automatically generated to capture all fields that are in the events ... This video explains the procedure for the