Media Summary: This video shows the lab solution of "2FA bypass using a bf attack" from Web Security Academy (Portswigger) A Simple writeup is posted on Medium - Disclaimer: The content shared in this video is intended ... This video is for Educational purposes only. Want me to train you for Practical courses and Global Certifications? or Want to hire ...
Pwsa Authentication 14 2fa Bypass Using A Brute Force Attack - Detailed Analysis & Overview
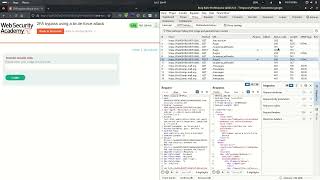
This video shows the lab solution of "2FA bypass using a bf attack" from Web Security Academy (Portswigger) A Simple writeup is posted on Medium - Disclaimer: The content shared in this video is intended ... This video is for Educational purposes only. Want me to train you for Practical courses and Global Certifications? or Want to hire ... During video we see how a weak protection against Learn Web App Pentesting for free, right in your browser ⏱️ Only 3 hours 🛠️ No VMs, no setup ... In this episode we will cover a vulnerability called
This video is for learning purpose only. Try this only on special environments. I'm not responsible for any unauthorized La autenticación de dos factores de este laboratorio es vulnerable a la fuerza bruta. Ya obtuvo un nombre de usuario y ...












![2FA Bypass Using a Brute-force Attack | [Turbo Intruder] [Burp CE] [2026]](https://i.ytimg.com/vi/k-jImgkx-xI/mqdefault.jpg)
![14: 2FA bypass using a brute-force attack || Bug Bounty POC $500 || Hacking Sikhe [IN HINDI]](https://i.ytimg.com/vi/w3W3ckzE5iI/mqdefault.jpg)
![[Hindi] Authentication vulnerabilities - Lab-2 | 2FA simple bypass | PortSwigger Labs | Tsecurity](https://i.ytimg.com/vi/xDr4pNHhfaI/mqdefault.jpg)



