Media Summary: Series of lectures on the Introduction to Lattices, Lattice Reduction, and Lattice-Based Welcome back to cryptography and network security Series in this video we'll be discussing about Subject : Computer Science Course Name : Quantum Algorithms and
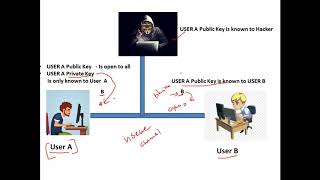
Public Key Cryptosystem Part 3 - Detailed Analysis & Overview
Series of lectures on the Introduction to Lattices, Lattice Reduction, and Lattice-Based Welcome back to cryptography and network security Series in this video we'll be discussing about Subject : Computer Science Course Name : Quantum Algorithms and Spies used to meet in the park to exchange code words, now things have moved on - Robert Miles explains the principle of ... Gate Smashers Shorts: Watch quick concepts & short videos here: Subscribe ... In this educational journey, we explore the intricacies of
Abroad Education Channel : Company Specific HR Mock ... In this lecture we will be looking at a brief introduction to