Media Summary: In this session, netspooky presents an introduction to Wanna learn to hack? Join: MY COURSES Sign-up for my FREE 3-Day C Course: ... Thanks again Hex Rays for sponsoring todays video! Get 50% off IDA Products at with code ...
Protocol Reverse Engineering - Detailed Analysis & Overview
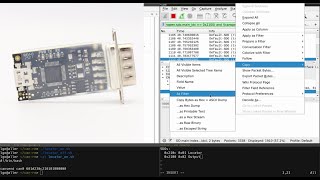
In this session, netspooky presents an introduction to Wanna learn to hack? Join: MY COURSES Sign-up for my FREE 3-Day C Course: ... Thanks again Hex Rays for sponsoring todays video! Get 50% off IDA Products at with code ... Join The Family: Check Out The Courses We Offer: ... In this video, we are using a cheap and open hardware CAN to USB adapter to sniff and analyze the CAN frames on an existing ... We are diving into the intricate world of mobile display
One of the essential skills for cybersecurity professionals is Dot dot will soon live. Maybe. Gotta make sure I can control the eyepiece from python. I bought this off-brand from the store and it doesn't have support! So I made my own 'drivers' for linux using ... I provide consultations regarding everything about hacking and In this episode we'll show how to use Chrome or Firefox along with Postman to go from a website using a private API all the way to ... 001 Network Training for Reverse Engineering and Malware Analysis - Part 1
MS17-010 is the most important patch in the history of operating systems, fixing remote code execution vulnerabilities in the world ...