Media Summary: Watch our short overview video to find out what are the In the latest edition of "A deep dive into the This is the first in a series of posts where
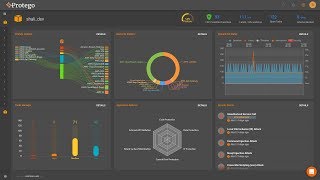
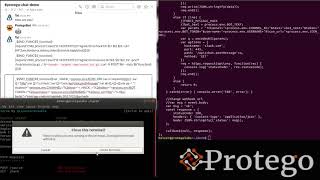
Protego Serverless Security - Detailed Analysis & Overview
Watch our short overview video to find out what are the In the latest edition of "A deep dive into the This is the first in a series of posts where Amazon Prime Video released an article explaining how they saved 90% on cloud computing costs by switching from ... In cloud-native environments in general, and OWASP Global AppSec Tel Aviv In moving to