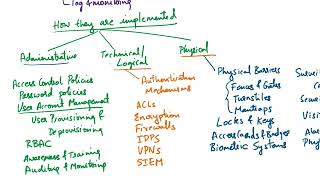
Media Summary: Get the threat intelligence guide → Learn about the technology → Exploring the ... Role-based access control (RBAC) is an essential method for managing permissions in cloud systems. In this video, Varun sir ... In this session, we break down one of the most critical topics in cybersecurity —
Protection Mechanisms Access Control Capability Based Systems Explained - Detailed Analysis & Overview
Get the threat intelligence guide → Learn about the technology → Exploring the ... Role-based access control (RBAC) is an essential method for managing permissions in cloud systems. In this video, Varun sir ... In this session, we break down one of the most critical topics in cybersecurity — Subscribe here: CyberPlatter Discord ... GATE Insights Version: CSE or GATE Insights Version: CSE ... I talk about a very simple set of resources that are sufficient for safely abstracting most of the underlying kernel resources.