Media Summary: Join me in this exciting video as we explore four powerful ways to use SQLmap for I found my first SQL Injection vulnerability and earned a €3600 bug bounty reward! 🚀 In this video, I ... I gave Claude code for a vulnerable app and told it to hack it. It dumped the entire database in under 2 minutes. In this video, I ...
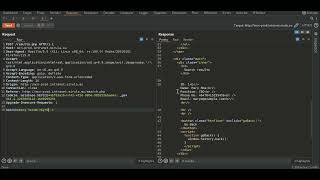
Post Based Sql Injection Bug Bounty Full Poc Exploit Tutorial - Detailed Analysis & Overview
Join me in this exciting video as we explore four powerful ways to use SQLmap for I found my first SQL Injection vulnerability and earned a €3600 bug bounty reward! 🚀 In this video, I ... I gave Claude code for a vulnerable app and told it to hack it. It dumped the entire database in under 2 minutes. In this video, I ... The software has a security flaw, specifically an unauthenticated blind Database Breached: The Power of SQL Injection IF you Enjoyed the video, don't forget to Like , Subscribe, and turn on the Notification Bell to stay updated! WHO AM I ? I'm ...
Tips and Tricks: SQL Injection (Bug Bounty Approach) Disclamer: The Video Content Has been made available informational and educational purposes only ... In the theme settings function of a web application, a dangerous loophole exists where any file can be uploaded without ...