Media Summary: We are given a COLLADA model (.dae file). We open that in Blender and dismantle the model to determine the gear ratio between ... Shows a small CoreWars program that crashes immediately by executing a DAT instruction. More info on CoreWars at: ... In this video we learn about Core Wars, a programming game where "warriors" try to destroy each other in a simulated computer ...
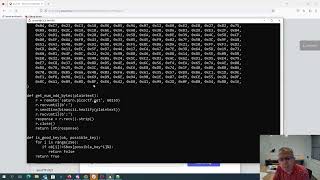
Picoctf 2023 Virtual Machine 0 - Detailed Analysis & Overview
We are given a COLLADA model (.dae file). We open that in Blender and dismantle the model to determine the gear ratio between ... Shows a small CoreWars program that crashes immediately by executing a DAT instruction. More info on CoreWars at: ... In this video we learn about Core Wars, a programming game where "warriors" try to destroy each other in a simulated computer ... 【Category Filter】 Reverse Engineering 【Original Event】 Use whois to find the administrative contact for an IP address (I am running whois from the Windows Subsystem for Linux, after ... kindly support me: If you would like to support me please , Subscribe ,Like and Share ...
Decompile an Android APK file using an online decompiler ( and find the flag in the resulting ... CTF Challenge Writeup 00:00 Intro 01:21 Dynamic Analysis 02:41 Ghidra Reversing 09:40 Whiteboard 17:20 Whiteboard 23:40 ... Hi Everyone, Michael here. Welcome to my walkthrough of my Used dnSpy ( to edit the Unity game to allow myself to fly over the wall and get the flag. Uses a one bit leak per encryption to break the encryption key, one byte at a time. # python 3 code from pwn import * import ... Flag is found in /etc/crontab, a file which keeps track of tasks that are run periodically on a linux server.
Grab a Corewars warrior from Corewars for Dummies ( and submit ... This is how I solved the Useless CTF challenge from the