Media Summary: As a continuation of the "Introduction to Windows Forensics" series, this episode looks at In this video, we delve into the world of cybersecurity and explore the key concepts of In this video I infect a VM with Nanocore malware and demonstrate some common techniques used by malware to survive the ...
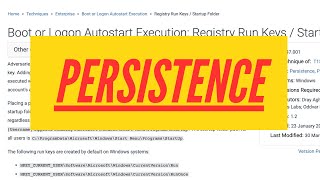
Persistence Mechanisms - Detailed Analysis & Overview
As a continuation of the "Introduction to Windows Forensics" series, this episode looks at In this video, we delve into the world of cybersecurity and explore the key concepts of In this video I infect a VM with Nanocore malware and demonstrate some common techniques used by malware to survive the ... This video covers an introduction into common malware Learn Cybersecurity and more with Just Hacking Training: See what else I'm up to with: ... In this full series we will talk about Incident Response and it will be a Free Training Course for everyone. Today is Day-17 and ...
In this video, I explore the process of establishing System Design for SDE-2 and above: System Design for Beginners: ... Request your Belkasoft X trial evaluation license for digital forensics, incident response, and eDiscovery: We ... The Sophos AI Assistant isn't just another AI tool. It's expertise from the team behind the world's leading MDR service, distilled into ... How do we stop ruminating or obsessive thoughts? Join Andrew Prince as he demonstrates how you can hunt for evidence of adversaries attempting to establish
In this follow-up webcast to Finding the Hidden Visitor - Phil 04:23 Why Adversaries Use Persistence 06:29 Welcome to Week 4 Lecture 2 of the course "Modern Application Development I" by Profs. Thejesh G N and Nitin ... Attackers abuse various Linux functionalities to maintain Windows 10 Security Demo – Reverse Shell, Be better than yesterday - In this video, we will be sharing several techniques and tactics used for obtaining