Media Summary: In this module, we'll be looking at Information Exposure. We will In this module, we'll be looking at Insecure Direct Object References. We'll In this module, we'll be looking at Remote File Inclusion. We will
Padding Oracle Attack Explainer Video Secure Code Warrior - Detailed Analysis & Overview
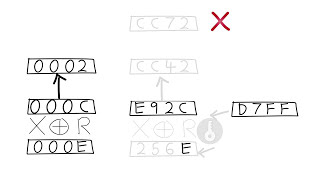
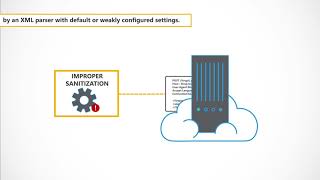
In this module, we'll be looking at Information Exposure. We will In this module, we'll be looking at Insecure Direct Object References. We'll In this module, we'll be looking at Remote File Inclusion. We will In this module, we'll be looking at Insufficient Anti-automation. We will In this module, we'll be looking at the Business Logic vulnerability. We will This is a demo for a school project that breaks a faulty Cipher Block Chain encryption. No one was hacked in the making of this ...