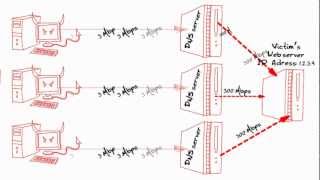
Media Summary: Attackers are taking advantage of weaknesses in the DNS protocol in order to launch a high bandwidth sophisticated Mobile apps house personal and confidential information for users across that world and hackers understand this making them a ... India and Pakistan are now engaged in a high-stakes
Operation Ababil Ddos Attacks Radware - Detailed Analysis & Overview
Attackers are taking advantage of weaknesses in the DNS protocol in order to launch a high bandwidth sophisticated Mobile apps house personal and confidential information for users across that world and hackers understand this making them a ... India and Pakistan are now engaged in a high-stakes Learn why organizations are struggling with Internet pipe saturation and how new