Media Summary: Have you ever wondered how malware defeats AV/EDR detection? Well, one of the common techniques used to prevent ... YOU CAN SUPPORT MY WORK BY BUYING A COFFEE ... I created this video to summarize the the first few chapters of the open source book Crypto101, which I have linked below.
Obfuscate Payloads With Xor Encryption - Detailed Analysis & Overview
Have you ever wondered how malware defeats AV/EDR detection? Well, one of the common techniques used to prevent ... YOU CAN SUPPORT MY WORK BY BUYING A COFFEE ... I created this video to summarize the the first few chapters of the open source book Crypto101, which I have linked below. Modern data protection requires more than simple bitwise transformations. In this project, we architect a modular Hi, XOR ciphers are simple & powerful. I explained What happens when your triage tools come up empty? In Lesson 5, we explore how threat actors hide their 'breadcrumbs of ...
Simple project to learn more about Python. I'm a beginner learning python and I had fun making it. Like and subscribe :) Try To Change The Pythonskript And The C++ Code To Get Your Hi Guys, today we want to see how to hack web servers and do some penetration tests in this playlist. We will use kali Linux and ... In this video series we'll analyse a Metasploit C# for Pentesters - Part II - Process Injection and Python3 for Offensive Pentest Thank You for watching Please share and Subscribe.
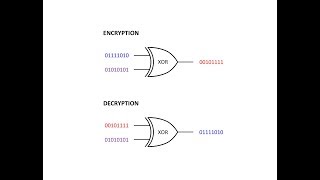
This video introduces an encryption technique ===