Media Summary: Here's a short scenario to help visualize the attack that sparked the need for Get a Free System Design PDF with 158 pages by subscribing to our weekly newsletter: More exclusive content: Twitter: Website: ...
Oauth 2 0 Pkce Explained Authentication Tokens Security Api Authentication - Detailed Analysis & Overview
Here's a short scenario to help visualize the attack that sparked the need for Get a Free System Design PDF with 158 pages by subscribing to our weekly newsletter: More exclusive content: Twitter: Website: ... If you're building a mobile app, single-page app (SPA), or browser-based tool that uses Free Resource: AWS Cheat Sheet covering 129 services : Ready to jumpstart your Cloud ... Become a senior software engineer with a job guarantee:
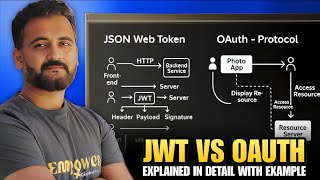
Hey everyone, In this video, we are going to understand OAuth 2.0 is a popular authorization framework used to secure APIs and applications in cloud computing. In this video, we’ll ... In this video, we do a complete deep dive into