Media Summary: Video taken during the Network and Distributed System Security ( SESSION Session 12C: Membership Inference Network and Distributed System Security ( SESSION 2B-2 SymQEMU: Compilation-based symbolic
Ndss 2017 Self Destructing Exploit Executions Via Input Perturbation - Detailed Analysis & Overview
Video taken during the Network and Distributed System Security ( SESSION Session 12C: Membership Inference Network and Distributed System Security ( SESSION 2B-2 SymQEMU: Compilation-based symbolic SESSION 6B-3 File Hijacking Vulnerability: The Elephant in the Room Files are a significant attack vector for security boundary ... SESSION 7A-2 ALchemist: Fusing Application and Audit Logs for Precise Attack Provenance without Instrumentation ... SESSION 3B-1 Chosen-Instruction Attack Against Commercial Code Virtualization Obfuscators Code virtualization is a ...
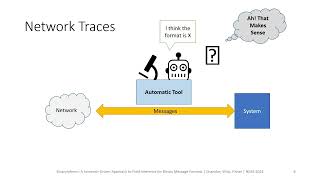
SESSION 7C-3 BinaryInferno: A Semantic-Driven Approach to Field Inference for Binary Message Formats We present ... SESSION 9B-2 On the Resilience of Biometric Authentication Systems against Random SESSION 2B-5 ExSpectre: Hiding Malware in Speculative