Media Summary: Gate Smashers Shorts: Watch quick concepts & short videos here: Subscribe ... Myself Shridhar Mankar a Engineer l YouTuber l Educational Blogger l Educator l Podcaster. My Aim- To Make Engineering ... Telegram group : contact me on Gmail at shraavyareddy810.com contact me on ...
Module 5 What Is Asymmetric Key Encryption - Detailed Analysis & Overview
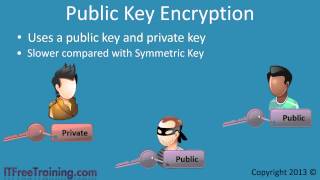
Gate Smashers Shorts: Watch quick concepts & short videos here: Subscribe ... Myself Shridhar Mankar a Engineer l YouTuber l Educational Blogger l Educator l Podcaster. My Aim- To Make Engineering ... Telegram group : contact me on Gmail at shraavyareddy810.com contact me on ... These two keys are mathematically related. They come as a pairs. The public key In this video, I endeavored to explain digital signatures in one minute, making it as quick and easy as possible.