Media Summary: A brief rundown of the possible rekindling of you know that moment where you step away from your computer for five minutes, come back, and windows has just restarted itself, ... In this video we'll be exploring how to attack, detect and defend against COM
Microsoft Com Hijacking - Detailed Analysis & Overview
A brief rundown of the possible rekindling of you know that moment where you step away from your computer for five minutes, come back, and windows has just restarted itself, ... In this video we'll be exploring how to attack, detect and defend against COM Get phishing into your next red team assessment or penetration test, and make it a breeze with Evilginx! Security researchers highlight a significant vulnerability in Disassemble, decompile and debug with IDA Pro! Use promo code HAMMOND50 for 50% off any IDA Pro ...
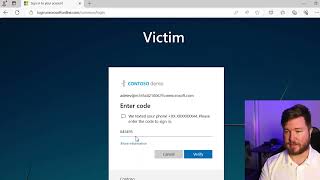
Phishing attacks are evolving, and even multi-factor authentication (MFA) is no longer foolproof. In this detailed demo, we ... Black Friday Sale! Get 20% off Altered Security training for Active Directory & Entra ID penetration ... Over 2.3 million users exposed through Google and Edge extensions. If you find this video interesting, ... Contact me on telegram if you need this page Telegram Channel . This video is a quick demonstration of COM In this video I discuss "dependency confusion" which was used to hack multiple private systems owned by Apple, Tesla,
In this video I talk about a recent attack called Reprompt that can be used to steal sensitive user data via More and more users and organisations are vulnerable as fraudsters accelerate their efforts to exploit vulnerabilities within ... Browser Hijackers are a nasty infection that ruins your browsing experience completely. In this video, you will know how to remove ... Google patches 79 Chrome vulnerabilities, new Windows zero-days called YellowKey and GreenPlasma are discovered, and ... Is your "Cloud-Only" Admin truly isolated? In this lab (EID-EXP-018), we demonstrate how a single misconfiguration in