Media Summary: Get phishing into your next red team assessment or penetration test, and make it a breeze with Evilginx! Want to uncover the latest insights on ransomware, dark web threats, and AI risks? Read the 2024 Threat Intelligence Index ... Discover how cybercriminals are exploiting link wrapping services to
Microsoft 365 Credential Theft Attacks - Detailed Analysis & Overview
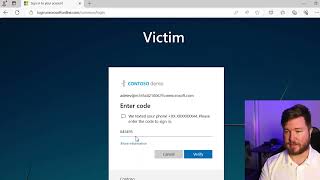
Get phishing into your next red team assessment or penetration test, and make it a breeze with Evilginx! Want to uncover the latest insights on ransomware, dark web threats, and AI risks? Read the 2024 Threat Intelligence Index ... Discover how cybercriminals are exploiting link wrapping services to They weren't hackers in a dark basement — they were running a business. RaccoonO365 was a phishing-as-a-service platform, ... In this video, I show you how to leverage the In this video, you'll learn how to investigate and act on email messages in
Disassemble, decompile and debug with IDA Pro! Use promo code HAMMOND50 for 50% off any IDA Pro ... In this video, I walk you through a comprehensive Token MFA alone is no longer enough to protect your users from modern phishing