Media Summary: In this video, we show you how to install Stop guessing and start analyzing. In this video, we dive into a classic Find your next cybersecurity career! CySec Careers is the premiere platform designed to connect candidates ...
Memory Forensics Analysis Process Injection Using Volatility - Detailed Analysis & Overview
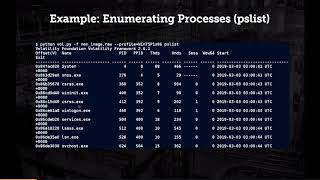
In this video, we show you how to install Stop guessing and start analyzing. In this video, we dive into a classic Find your next cybersecurity career! CySec Careers is the premiere platform designed to connect candidates ... This presentation mainly focuses on the practical concept of What do you do when you know there is more to the story than what the tool is reporting back to you? This presentation will walk ... This video is part of the presentation "Reversing and Investigating Malware Evasive Tactics - Hollow
... in plaintext so it's a good opportunity for us to Ever wondered how investigators catch malware that hides deep inside system Welcome to **Cyberhawk Consultancy**, where we turn complex digital




![RAM Analysis with Volatility Workbench | Easy Memory Forensics Tutorial [Hindi]](https://i.ytimg.com/vi/N6MxUZmpmqI/mqdefault.jpg)