Media Summary: This is the University of Utah's undergraduate course on Two huge security issues found in almost all modern processors. How do they work and what can we do about it? Let's find out! In this video, Unbounded Systems co-founder Manish Vachharajani explains the
Meltdown Explained Cs Ece 3810 Computer Organization - Detailed Analysis & Overview
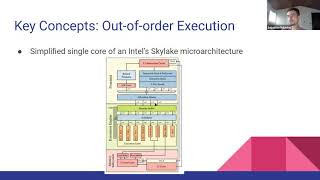
This is the University of Utah's undergraduate course on Two huge security issues found in almost all modern processors. How do they work and what can we do about it? Let's find out! In this video, Unbounded Systems co-founder Manish Vachharajani explains the Insomni'hack 2018 Title: Microarchitectural Attacks and the Case of