Media Summary: We test and analyse a "scantime crypter" whilst explaining the terminology behind it. In this video, I reverse engineer the UnixStealer infostealer and walk through the We analyse the code of our unpacked Alpha ransomware sample and find a flaw in the
Malware Analysis Exploring Spora S Encryption Procedure - Detailed Analysis & Overview
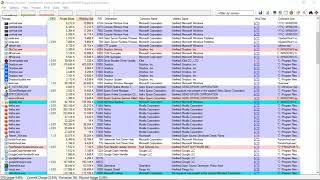
We test and analyse a "scantime crypter" whilst explaining the terminology behind it. In this video, I reverse engineer the UnixStealer infostealer and walk through the We analyse the code of our unpacked Alpha ransomware sample and find a flaw in the A quick showcase of unpacking a Locky ransomware sample. This is not the quick-and-dirty TryHackMe Masquerade walkthrough where we speedrun answers. In this video, I walk through the ... Unpacking a NanoCore RAT using DnSpy and MegaDumper.
In this first part we unpack a .NET based We create a decrypter for Alpha ransomware. In this video, we dive into the basics of Hackers don't always need to break your data today. Many are already collecting In this video, we demonstrate how REVEN makes it possible to connect data sent through the network with the code that ...