Media Summary: WLAN networks can also restrict access to known macspoof Welcome to come hackingeducation, a full guide to Please consider supporting my channel! ✨ Every bit helps—whether
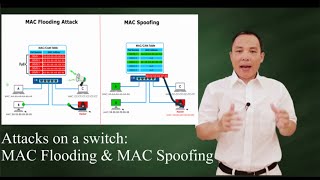
Mac Spoofing Explained Ethical Hacking Cyber Security - Detailed Analysis & Overview
WLAN networks can also restrict access to known macspoof Welcome to come hackingeducation, a full guide to Please consider supporting my channel! ✨ Every bit helps—whether Yes, WLAN operators can track you using your


![[Hindi] What is MAC Address and MAC Spoofing? #cybersecurity](https://i.ytimg.com/vi/JcR4rZhOgpU/mqdefault.jpg)