Media Summary: An oldie but a goodie, Dr Mike Pound revisits the In this episode of Whiteboard Wednesday, John Wagnon discusses the Entire course: ➡️ ⏰ Timestamps for ...
Logjam Tls Vulnerablity - Detailed Analysis & Overview
An oldie but a goodie, Dr Mike Pound revisits the In this episode of Whiteboard Wednesday, John Wagnon discusses the Entire course: ➡️ ⏰ Timestamps for ... To get better at system design, subscribe to our weekly newsletter: Checkout our bestselling System Design ... Video recording of Kenny Paterson's lecture (Part 1) at the COST Action IC1306 School on Cryptographic Attacks held in Porto on ... Can encryption be strong and weak at the same time? In 2015,
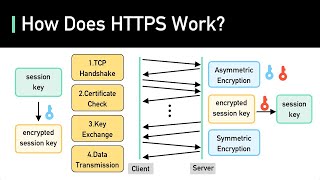
Hosts: Steve Gibson with Leo Laporte Let's Encrypt's Terms of Service, more on "plane hacker" Chris Roberts, a major new ... This is the 2nd Episode of Security Talk in which we discuss and present our take on some of the recent news in the Security ... How does your computer arrange with a server to start talking in code? Dr Mike Pound explains the Recorded at AppSecUSA 2016 in Washington, DC HTTPS & Proactive website and SSL certificate monitoring: ... Earlier this year, we discovered that Diffie-Hellman key exchange – cornerstone of modern cryptography – is less secure in ...
Video recording of Kenny Paterson's lecture (Part 2) at the COST Action IC1306 School on Cryptographic Attacks held in Porto on ... Warning! We go deep in this video to explain how the In this video, we explore mTLS (Mutual Transport Layer Security) and why it's a critical tool for securing communications where ...





![SSL/TLS Vulnerability Scan (sslscan) using Linux [KALI/Rocky/Ubuntu]](https://i.ytimg.com/vi/t_lB7vje_Hk/mqdefault.jpg)