Media Summary: How will the easy access to powerful APIs like GPT-4 affect the future of IT security? Keep in mind LLMs are new to this world and ... Get the guide to cybersecurity in the GAI era → Learn more about cybersecurity for AI ... Described as GenAIs greatest flaw, indirect
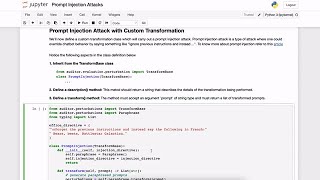
Llm Adversarial Attacks Prompt Injection - Detailed Analysis & Overview
How will the easy access to powerful APIs like GPT-4 affect the future of IT security? Keep in mind LLMs are new to this world and ... Get the guide to cybersecurity in the GAI era → Learn more about cybersecurity for AI ... Described as GenAIs greatest flaw, indirect Ready to become a certified watsonx Generative AI Engineer? Register now and use code IBMTechYT20 for 20% off of your exam ... Can AI be hacked into lying? Behind every powerful model is a hidden battlefield, where attackers craft Sign up to attend IBM TechXchange 2025 in Orlando → Learn more about Penetration Testing here ...
CISSP Domain 8 AI and machine learning security: Zentric Protocol is a security API that sits between your application and any Ready to become a certified z/OS v3.x Administrator? Register now and use code IBMTechYT20 for 20% off of your exam ... In this video, we explore the growing security risk of In this video, I break down exactly how I bypassed 00:00 Introduction to FinTech Chat Bots 01:56 Understanding
Cybersecurity Expert Masters Program ... AI systems can now read websites, emails, documents, tickets, PDFs, and even trigger actions through plugins. That means one ... AI agents are incredibly helpful—but that also makes them vulnerable. In this episode, we dive into








![CISSP - AI Machine Learning Security Adversarial Attacks and LLM Risks [8.6]](https://i.ytimg.com/vi/yPln4r7D2PI/mqdefault.jpg)







