Media Summary: Hi, hope you are doing well This video is to show how steps can be chained to achieve an powerful Learn Cybersecurity and more with Just Hacking Training: See what else I'm up to with: ... cybersecurity Welcome back! In this video, we dive deep into the TryHackMe Hide and Seek room, ...
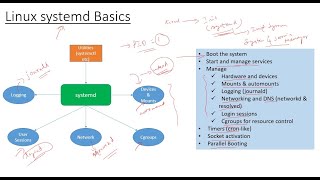
Linux Systemd Persistence With Backdoor - Detailed Analysis & Overview
Hi, hope you are doing well This video is to show how steps can be chained to achieve an powerful Learn Cybersecurity and more with Just Hacking Training: See what else I'm up to with: ... cybersecurity Welcome back! In this video, we dive deep into the TryHackMe Hide and Seek room, ... In this video we will demonstrate a basic way to create a Read the full technical breakdown of PeerBlight and the React2Shell attack chain: ... Mentorship/On-the-Job Support/Consulting - or me.com ...