Media Summary: In this video we try solving picoCTF's NewOverflow2 challenge using an unusual way! we try ROP and bypass arguments checks ... In previous weeks, we've gone over techniques like shellcoding to inject our own malicious code into an executable, but many of ... There are a lot of tutorials on ROP out there, so I try to explain the concept in a different way. Maybe that's a bad idea and a lot ...
Lesson 2 Return Oriented Programming And More - Detailed Analysis & Overview
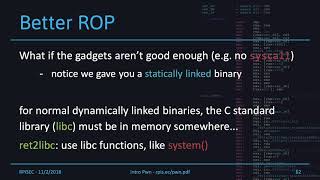
In this video we try solving picoCTF's NewOverflow2 challenge using an unusual way! we try ROP and bypass arguments checks ... In previous weeks, we've gone over techniques like shellcoding to inject our own malicious code into an executable, but many of ... There are a lot of tutorials on ROP out there, so I try to explain the concept in a different way. Maybe that's a bad idea and a lot ... Hi guys my name is Alex and I'm going to give a brief introduction to Let's learn some historical context behind ROP! Module information at pwn.college/modules/rop. Help the channel grow with a Like, Comment, & Subscribe! ❤️ Support ➡ ↔
Let's learn about some specific techniques for ROP! Module information at How do we spawn a shell if ASLR is enabled and the stack is made non-executable? Or, even how to create and run python script using python IDLE Detail Video On How to ...