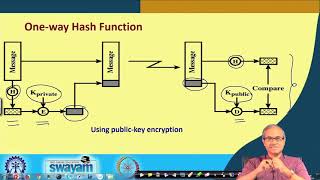
Media Summary: Link for playlists: Link for our website: ... Course : B.C.A Semester : V SEM Subject : NETWORK SECURITY Chapter Name : Lecture 32 Cryptographic hash functions Part II
Lecture 32 Whirpool Cryptographic Hash Function - Detailed Analysis & Overview
Link for playlists: Link for our website: ... Course : B.C.A Semester : V SEM Subject : NETWORK SECURITY Chapter Name : Lecture 32 Cryptographic hash functions Part II Bitcoin and Cryptocurrency Technologies Online Course