Media Summary: Ever wanted to be able to modify a program to arbitrarily execute your own code? Well you're in luck! Watch our workshop on ... Join Jeremy as he goes over the basics of buffer overflows, and Hi there! New to Ethical Hacking? If so, here's what you need to know -- I like to share information a LOT, so I use this channel to ...
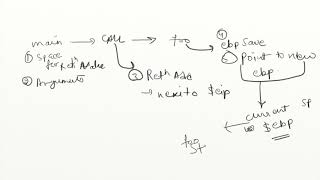
Lecture 1 Binary Exploitation Elf Memory Stack Organization Hindi - Detailed Analysis & Overview
Ever wanted to be able to modify a program to arbitrarily execute your own code? Well you're in luck! Watch our workshop on ... Join Jeremy as he goes over the basics of buffer overflows, and Hi there! New to Ethical Hacking? If so, here's what you need to know -- I like to share information a LOT, so I use this channel to ... Welcome to the training and talks of InCTF and InCTFj 2021. The schedule is posted on our site, social media, and Discord server. Hello everyone. This video is a crucial part of my buffer overflow series where I am running a simple program written in C ... Hosted by DePaul Security Daemons ( Speaker: Alejandro Salinas, Associate Security Consultant at NCC ...
This video is a recorded version of free LIVE online training delivered by and supported by www.theoffensivelabs.com ... Our engineering director Huck explains the basics of









![[HINDI] Introduction to Buffer Overflows | Writing an Exploit | Part #1 : Fuzzing](https://i.ytimg.com/vi/ZYSfsHk6esE/mqdefault.jpg)




