Media Summary: All my videos are for educational purposes with bug bounty hunters and penetration testers in mind YouTube don't take down my ... LIKE and SUBSCRIBE with NOTIFICATIONS ON if you enjoyed the video! If you want to learn bug bounty hunting from me: ... Membership // Want to learn all about cyber-security and become an ethical
Jwt Hacking Json Web Token - Detailed Analysis & Overview
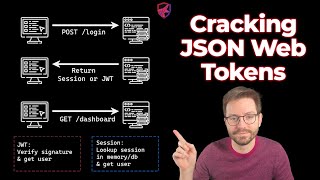
All my videos are for educational purposes with bug bounty hunters and penetration testers in mind YouTube don't take down my ... LIKE and SUBSCRIBE with NOTIFICATIONS ON if you enjoyed the video! If you want to learn bug bounty hunting from me: ... Membership // Want to learn all about cyber-security and become an ethical This playlist has a list of free videos from the course " For educational purposes ONLY Sign up to HacktheBox for cybersecurity training and CTF's: ... In this video, I have explained the Broken Access Control vulnerability, which is a common vulnerability to be found on APIs.
If you would like to support the channel and I, check out Kite! Kite is a coding assistant that helps you code faster, on any IDE offer ... Dear Defronixters !! This is the 50th Class (half century) of our Bug Bounty Complete Free Capsule Course by Defronix Cyber ... Hello everyone. In this video I will introduce to you the concept of THIS VIDEO IS FOR EDUCATIONAL PURPOSES ONLY. I DO NOT ENCOURAGE OR SUPPORT ILLEGAL ACTIVITY** Welcome to JayPMedia, your go-to channel for animated, easy-to-understand explanations of developer topics! We basically ... In this video we'll see: 0:00 Intro What is










![Day-50 JWT Attack - JSON Web Tokens Part 1 - Bug Bounty Free Course [ Hindi ]](https://i.ytimg.com/vi/mUpSuINhYl4/mqdefault.jpg)
![[HINDI] Introduction to JWT | JSON Web Token | Security Concerns of JWT](https://i.ytimg.com/vi/5mUDRQfwXuE/mqdefault.jpg)






