Media Summary: 00:00 intro 00:25 JWT primer 01:54 JWT vs SessionIDs 03:30 Code review 06:25 Testing our JWT 09:02 LIKE and SUBSCRIBE with NOTIFICATIONS ON if you enjoyed the video! If you want to learn bug bounty hunting from me: ... This playlist has a list of free videos from the course "
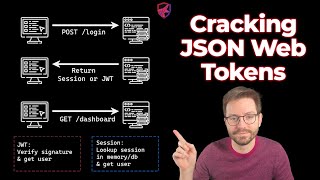
Cracking Json Web Tokens - Detailed Analysis & Overview
00:00 intro 00:25 JWT primer 01:54 JWT vs SessionIDs 03:30 Code review 06:25 Testing our JWT 09:02 LIKE and SUBSCRIBE with NOTIFICATIONS ON if you enjoyed the video! If you want to learn bug bounty hunting from me: ... This playlist has a list of free videos from the course " All my videos are for educational purposes with bug bounty hunters and penetration testers in mind YouTube don't take down my ... Membership // Want to learn all about cyber-security and become an ethical hacker? Join this channel now to gain access into ... In this 10-minute video, I will explain what
For educational purposes ONLY Sign up to HacktheBox for cybersecurity training and CTF's: ... In this video, I have explained the Broken Access Control vulnerability, which is a common vulnerability to be found on APIs. In this video we are performing a penetrationtest of a JWT by In this video, you will hack a vote feature by exploiting a JWT implementation weakness using two BurpSuite extensions: Hey everyone, In this video, we are going to talk about PASETO Tokens which tent to replace JWT ( If you would like to support the channel and I, check out Kite! Kite is a coding assistant that helps you code faster, on any IDE offer ...