Media Summary: Disclaimer:- This video is for Educational purposes only . Copyright disclaimer under section 107 of the Copyright Act , 1976 ... In this tutorial, we develop an application that executes the TechRanch Welcome to Tech-Ranch! A place where we learn and earn technical skills in the most efficient way. Today we are ...
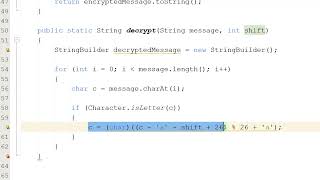
Java Source Code For Encryption And Decryption Of Ceaser Cipher - Detailed Analysis & Overview
Disclaimer:- This video is for Educational purposes only . Copyright disclaimer under section 107 of the Copyright Act , 1976 ... In this tutorial, we develop an application that executes the TechRanch Welcome to Tech-Ranch! A place where we learn and earn technical skills in the most efficient way. Today we are ... OFF ANY Springboard Tech Bootcamps with my Hook Security isn't an afterthought — it's a requirement. From securing user passwords with hashing to You're literally one click away from a better setup — grab it now! As an Amazon Associate I earn ...
Output at : 3:45 Assignment for Mr. Maruf Hassan sir. Course: Information System Security Course Code: SE 332 A