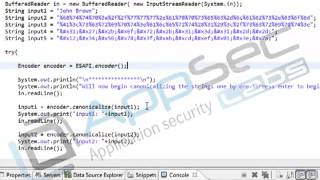
Media Summary: ... clearly see that error conditions end up with the input from that three-digit access Now of course comes the real test I've put in that HTML And I want to make sure that no one creates a username that could potentially contain a
Java Secure Coding Output Encoding 7 2 Reflected Xss Attacks - Detailed Analysis & Overview
... clearly see that error conditions end up with the input from that three-digit access Now of course comes the real test I've put in that HTML And I want to make sure that no one creates a username that could potentially contain a ... canonicalize function whether I just want to use the View Notes Here - In this video, I have explained and ... ... how that works in a browser So you can see directly accessing file 1.txt works and again you can do file