Media Summary: Java Secure Coding: Input Validation 2 1 Logic Flaws You can buy me a coffee if you want to support the channel: In this video, we will explore the ... View Notes Here - In this video, I have explained and ...
Java Secure Coding Input Validation 2 2 Command Injection - Detailed Analysis & Overview
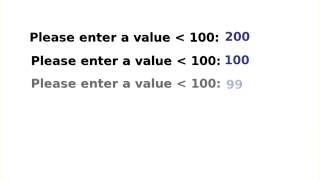
Java Secure Coding: Input Validation 2 1 Logic Flaws You can buy me a coffee if you want to support the channel: In this video, we will explore the ... View Notes Here - In this video, I have explained and ... ... age so as long as I enter an integer again everything is fine passes This video is part of an online course, Intro to Stay ahead of cybersecurity insights – Subscribe & turn on notifications! Let's learn about a neat trick you should know when ...
Join me live on Sunday May 10th for a deep dive into Chapter