Media Summary: In this video, we look into Poor code quality vulnerability. Android Pentest Series : In this video, we look into Insufficient cryptography vulnerability. Follow us Android applications aaj har business ka core ban chuki hain — banking, fintech, e-commerce, healthcare, ed-tech, aur ...
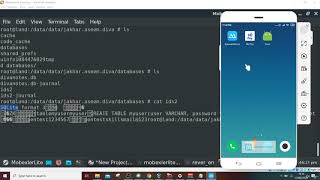
Insecure Authentication Androidpentesting Owasp Top 4 Mobile - Detailed Analysis & Overview
In this video, we look into Poor code quality vulnerability. Android Pentest Series : In this video, we look into Insufficient cryptography vulnerability. Follow us Android applications aaj har business ka core ban chuki hain — banking, fintech, e-commerce, healthcare, ed-tech, aur ... In this video, we look into Extraneous Functionality vulnerability. Follow us This course includes customized VM with pre-installed tools which will save your time in installing multiple tools required Hi everyone , I'm Gowry, and welcome back to my channel! In today's video, we'll explore
In this video, we show what things make an android app vulnerable to "Improper Platform usage" and how to mitigate it. Follow us ...