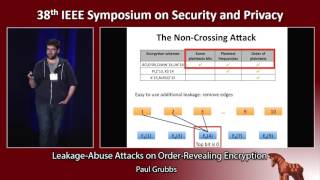
Media Summary: IEEE Security and Privacy 2018 Hacking conference , , , , , . Security researchers and practitioners have proposed many techniques for securely storing and Sep 9, 2020 Zoom conference IEEE Euro S&P 2020 Session : Privacy 1 Practical Volume-Based
Improved Reconstruction Attacks On Encrypted Data Using Range Query Leakage - Detailed Analysis & Overview
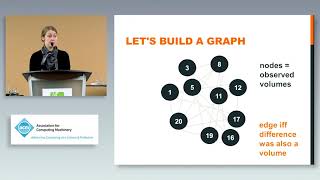
IEEE Security and Privacy 2018 Hacking conference , , , , , . Security researchers and practitioners have proposed many techniques for securely storing and Sep 9, 2020 Zoom conference IEEE Euro S&P 2020 Session : Privacy 1 Practical Volume-Based The 7th BIU Winter School on Cryptography- Differential Privacy: CCS 2020: Full Database Reconstruction in Two Dimensions A presentation on "Understanding database
Authors: Sina Shaham, Gabriel Ghinita and Cyrus Shahabi Abstract: Most online mobile services make Visit our website to download the slides and see upcoming webinars: ... Shiva Kasiviswanathan, GE Global Research Big














![[Session 5] Enhancing the Performance of Spatial Queries on Encrypted Data through Graph Embedding](https://i.ytimg.com/vi/_utGf95gG6k/mqdefault.jpg)

