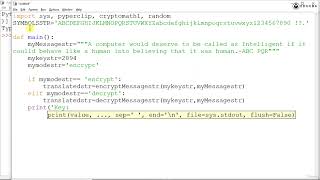
Media Summary: We use a brute-force attack to hack a message encrypted with the We write a program to encrypt and decrypt messages using the Encrypted and decrypted texts are printed to the console.
Implementation Of Affine Cipher In Python - Detailed Analysis & Overview
We use a brute-force attack to hack a message encrypted with the We write a program to encrypt and decrypt messages using the Encrypted and decrypted texts are printed to the console. We cover two new, more secure ciphers: The multiplicative and Affine Cipher (Encryption - Decryption - Python code) Implementation of Affine Cipher in Python
Artificial intelligence please subscribe. Affine Cipher Encryption Technique with Example