Media Summary: In this video, focusing on the intricacies of # PendingIntent, the advanced version of normal In this video you'll learn about explicit & implicit
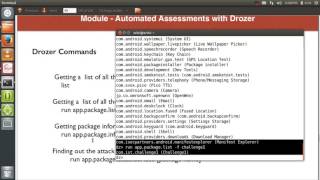
How To Exploit Android Intent Android Exploitation Intent - Detailed Analysis & Overview
In this video, focusing on the intricacies of # PendingIntent, the advanced version of normal In this video you'll learn about explicit & implicit In this video we're gonna have a look at how Checkout this link for the best practice for protected In this video I analyze how NASA's mobile app “Spot the Station” exposes an exported
This video shows what kind of Exported Activities can be Pixnapping is a new class of attacks that allows a malicious Protect and defend your own mobile applications with Guardsquare! Learn ... M8 – Security Decisions via untrusted inputs Intent Spoofing 2372580 By Daniele Gallingani "We identified a set of vulnerabilities that common