Media Summary: Ready to become a certified Qiskit Developer? Register now and use code IBMTechYT20 for 20% off of your exam ... This is a live demonstration of an automated
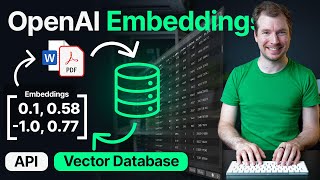
How Ai Vector Databases Detect Cyber Threats In Real Time - Detailed Analysis & Overview
Ready to become a certified Qiskit Developer? Register now and use code IBMTechYT20 for 20% off of your exam ... This is a live demonstration of an automated